An overview of two-factor authenticatation (2FA) and how it works.
What is two-factor authentication (2FA) and multi-factor authentication (MFA)?
Multi-factor authentication (MFA), which includes the well known two-step verification or two-factor authentication (2FA), is a method for granting a user access to an online account. This method requires, that the user can pass one or more challenges, known as factors, before access to the account will be granted by the authentication mechanism of the service. These factors are of different nature and ensures, that the user has a certain location, knowledge, possession or inherence.
Examples of authentication factors.
An example of the location factor is the computer network, that is associated with an account. This factor has not been widely available in web-based social media platforms, such as Facebook and Instagram, but it has been commonly used by servers and firewalls to restrict access by location to systems and network services for decades. The location factor is typically followed up with a possession factor or knowledge factor.
An example of the knowledge factor is the well known combination of the username and password, that is associated with an account. If this is the only factor, also known as single-factor authentication (SFA), then the account can be vulnerable to guessing, discovery or network monitoring. Read more about this later.
An example of the possession factor is a secret key, that is associated with an account. In Denmark, the state issued NemID key code card, NemID key file and MitID app are all possession factors, that are used in combination with username and password.
An example of the inherence factor is a biometric fingerprint or face detection. These are commonly used with smartphones for unlocking the screen. This factor can be vulnerable to unconcented forced authentication.
How to enable two-factor authentication (2FA) or multi-factor authentication (MFA) for Facebook, Instagram and other online accounts.
Follow this procedure, step by step, to protect online accounts with 2FA and MFA.
- Log in to Facebook, Instagram or other online account, which should be protected by two-factor authentication or multi-factor authentication. Find the settings and configuration page for security and authentication.
- If the current email address, that is associated with the account, is insecure or no longer used, then change it at this point. This can become important in the event of account recovery and it also protects the account from being taken over by someone, that abuses the forgot password feature.
- If the current password is weak or compromised, then change it at this time. I recommend, that my password generator is used to create a unique random password.
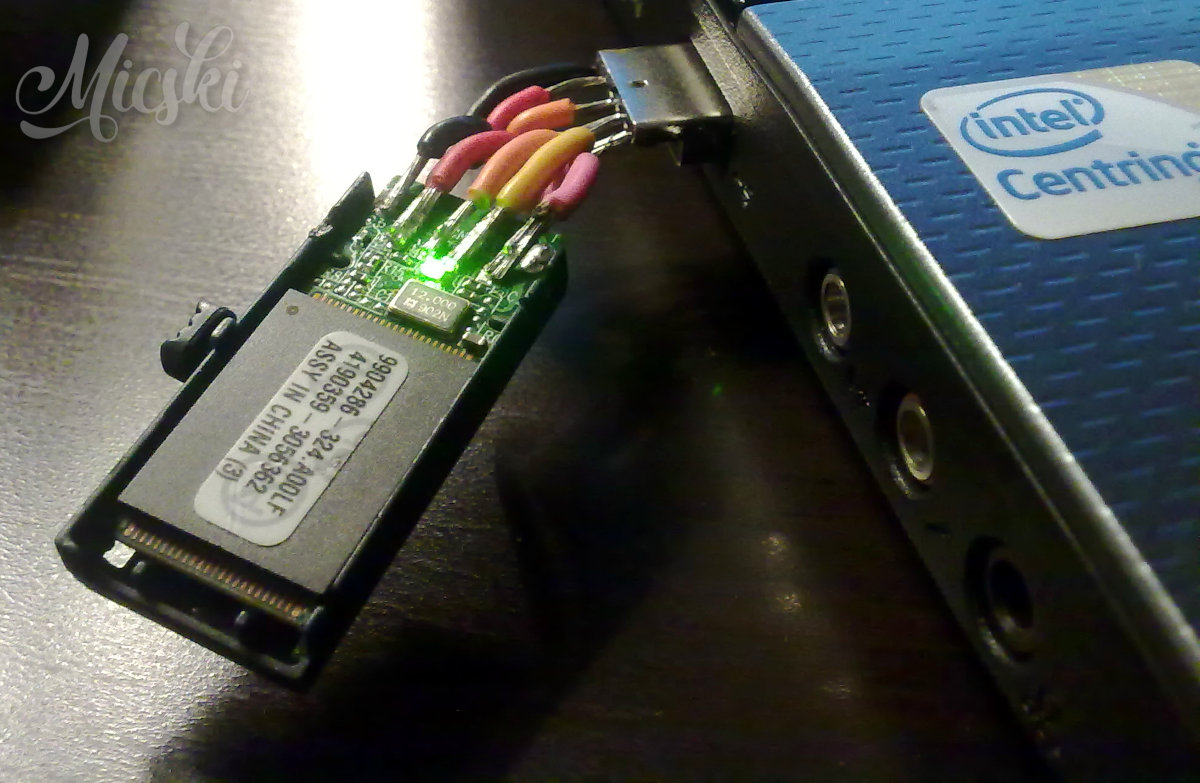
- Enable one or more additional authentication factors, such as the use of an authentication app. This factor is known as the possession factor, because it will require the user to possess a shared secret key, which will be used to generate short one-time codes, that has to be entered, when logging in from an unknown device or network.
- Make sure, that a backup method is available. This often comes in the form of one or more plain text based recovery codes, that can be stored in a secure place, such as on an encrypted file system or written on paper and stored in a physical vault. If the additional authentication factors should fail or no longer be available, this backup method can be used to gain access instead.
How someone can guess, discover or hack a username and password.
If only a username and password is necessary for accessing an account, also known as the knowledge factor in single-factor authentication (SFA), then it might be possible for someone to guess, discover or hack the username or password. The purpose of this is often blackmail or identity theft with fraud in mind.
Someone, that knows the user, might be able to out-right guess the username and guess the password. Others can use special software, that either guesses or loads a long list of well-known or leaked passwords and then tries each one until access is gained.
Someone might also discover the username and password by looking over a shoulder, listening over a conversation or monitoring the network traffic. An example of network monitoring is someone with a computer and software, that can capture the data packets, that is transmitted from computers and smartphones in the same local area network, such as the wireless network in a public café. The captured data packets are then processed with the purpose of discovering usernames and passwords.
If the methods above failed, someone might try to hack the username and password instead. A common example of this is, that someone gets in possession or control of a storage medium, that contains the username and password. This could be a computer which contains a harddisk with a note or document, that contains the username and password. The computer can then be booted from a specially prepared USB key, or the harddisk can then be moved to another computer, both of which can bypass the operating system and read the file system and content directly. This could also be a smartphone, that contain the username and password in an installed password manager app or browser feature, while being either stolen in unlocked state, unlocked by forced fingerprint or unlocked by PIN, that can be derived from filthy glass.
More about MFA and 2FA.
Multi-factor authentication on Wikipedia.
